What is a Buffer Overflow, Attack Types and Prevention Methods
By A Mystery Man Writer
Last updated 16 Jul 2024

Attackers exploit buffer overflow issues to change execution paths, triggering responses that can damage the applications and exposes private information.

Buffer Overflow Basics

What is a Buffer Overflow Attack Types and Prevention Methods
How to Detect and Prevent Buffer Overflow Attacks in a Database

What is Buffer Overflow? Buffer Overflow Attack - ManageEngine

What Is a Buffer Overflow

Buffer Overflow Basics
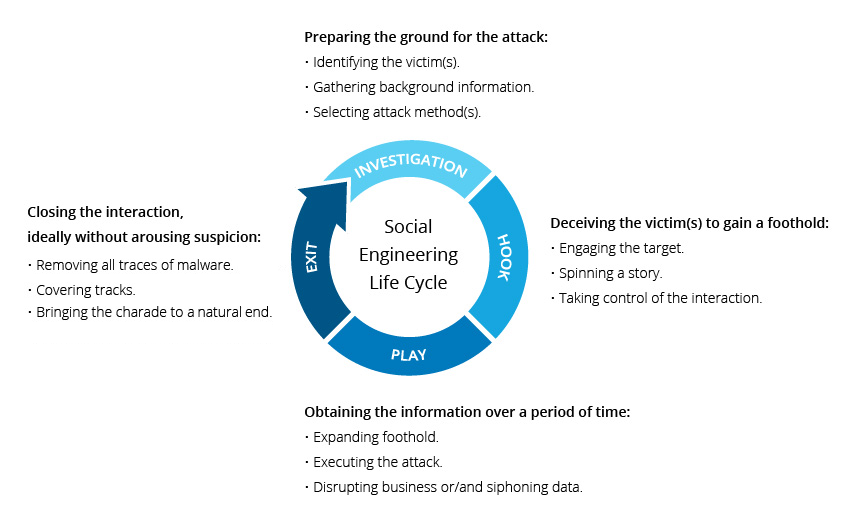
What is Social Engineering Attack Techniques & Prevention
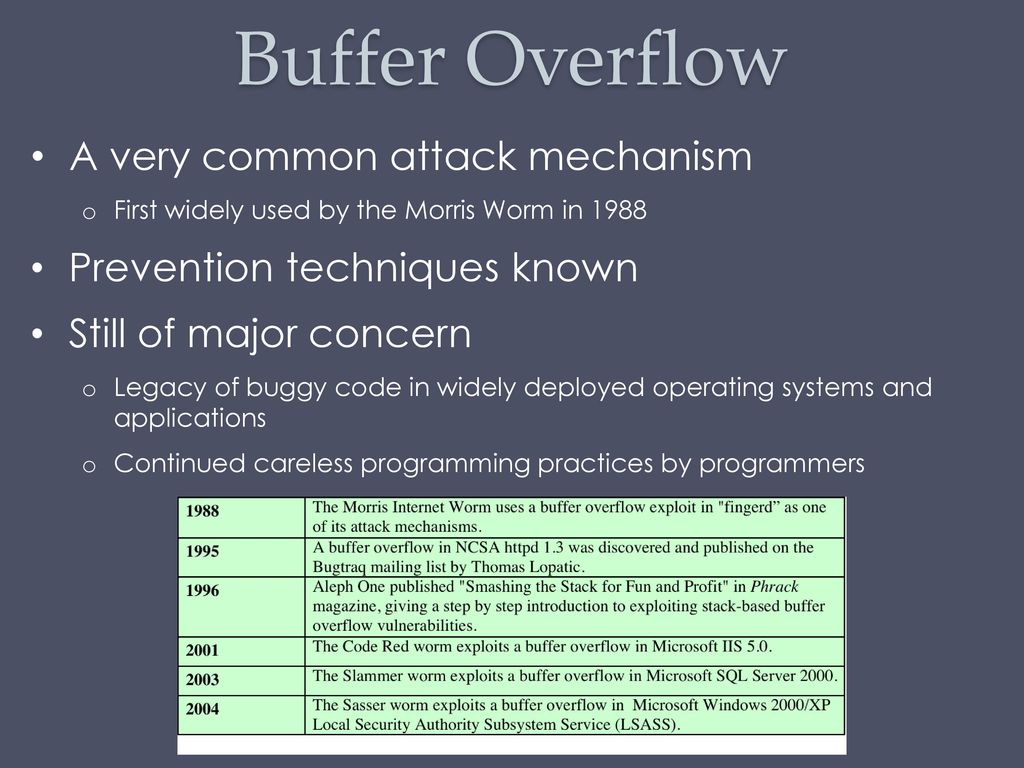
Buffer Overflow & Software Security - ppt download

ROP and Buffer Overflow: A Deadly Duo in Cybersecurity Exploits

Stack-Based Buffer Overflows on Linux x86 Course

What is a Buffer Overflow, Attack Examples and Prevention Methods
Recommended for you
You may also like