Token tactics: How to prevent, detect, and respond to cloud token
By A Mystery Man Writer
Last updated 15 Jul 2024
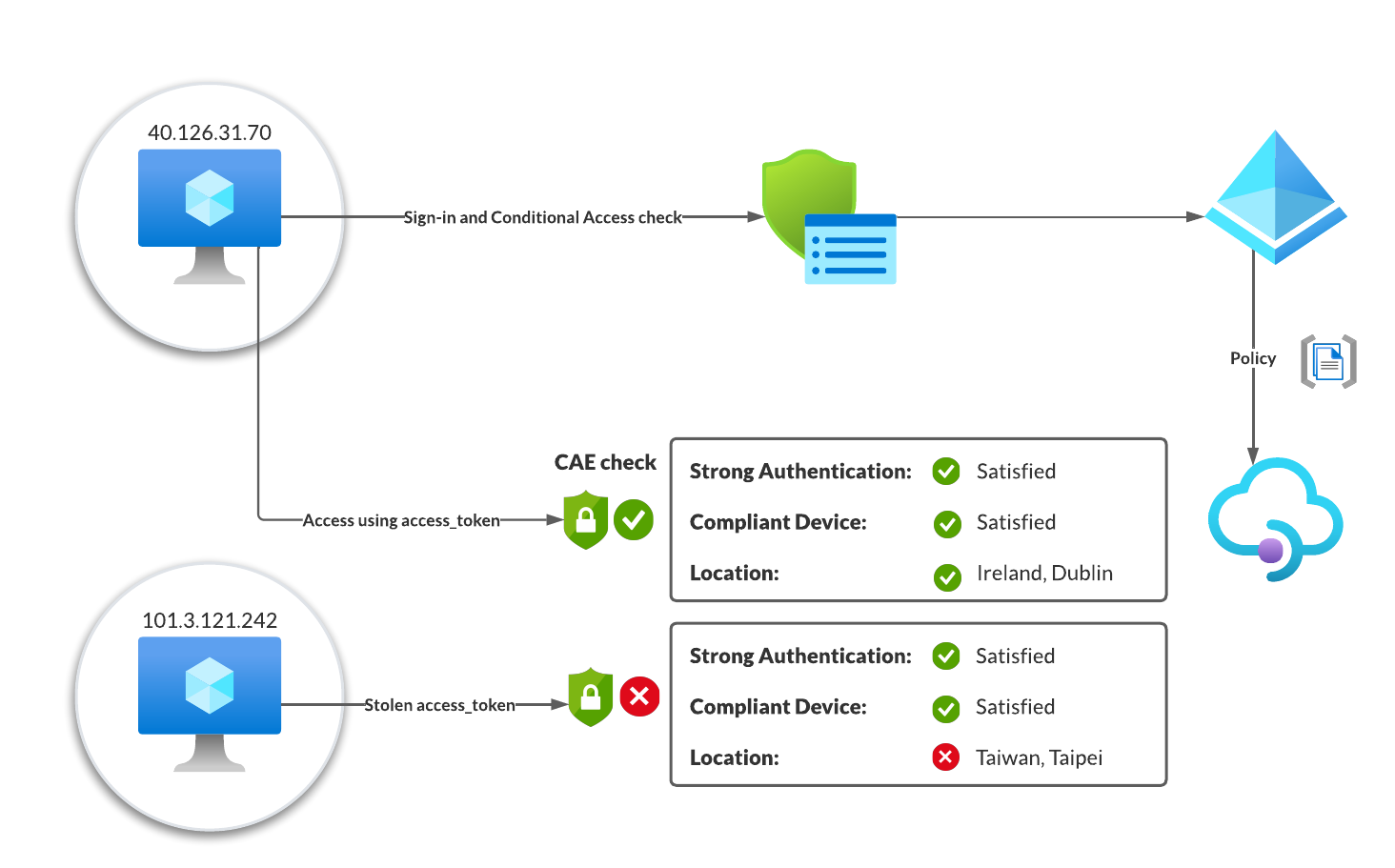
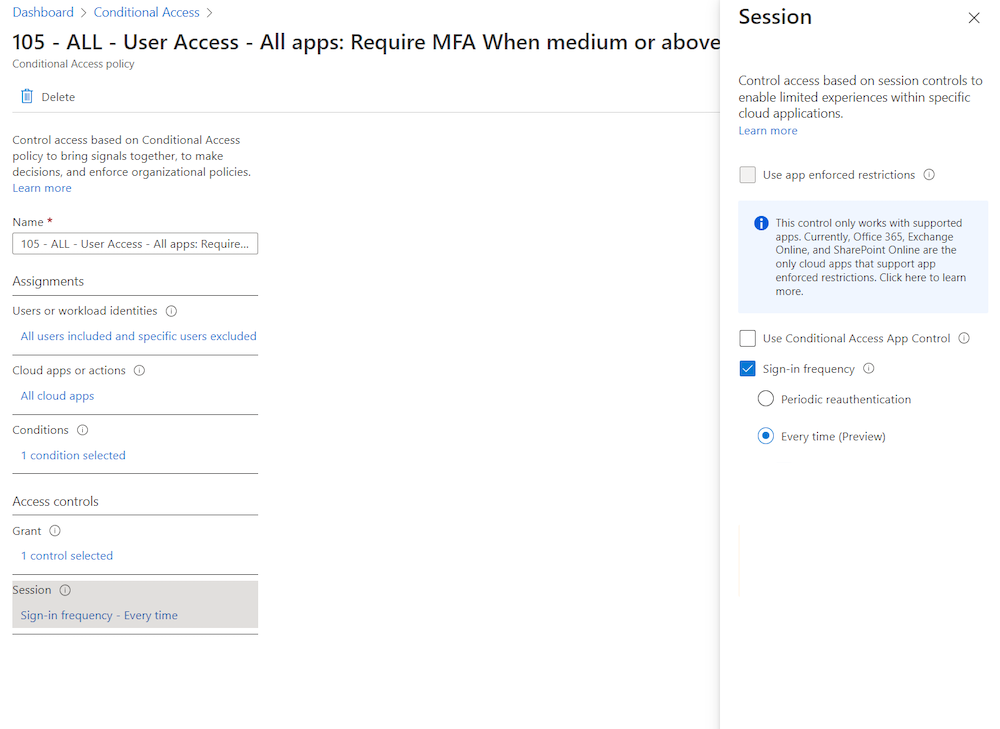
Continuous access evaluation - Cloudbrothers

Matthew Zorich en LinkedIn: Total Identity Compromise: DART lessons on securing Active Directory
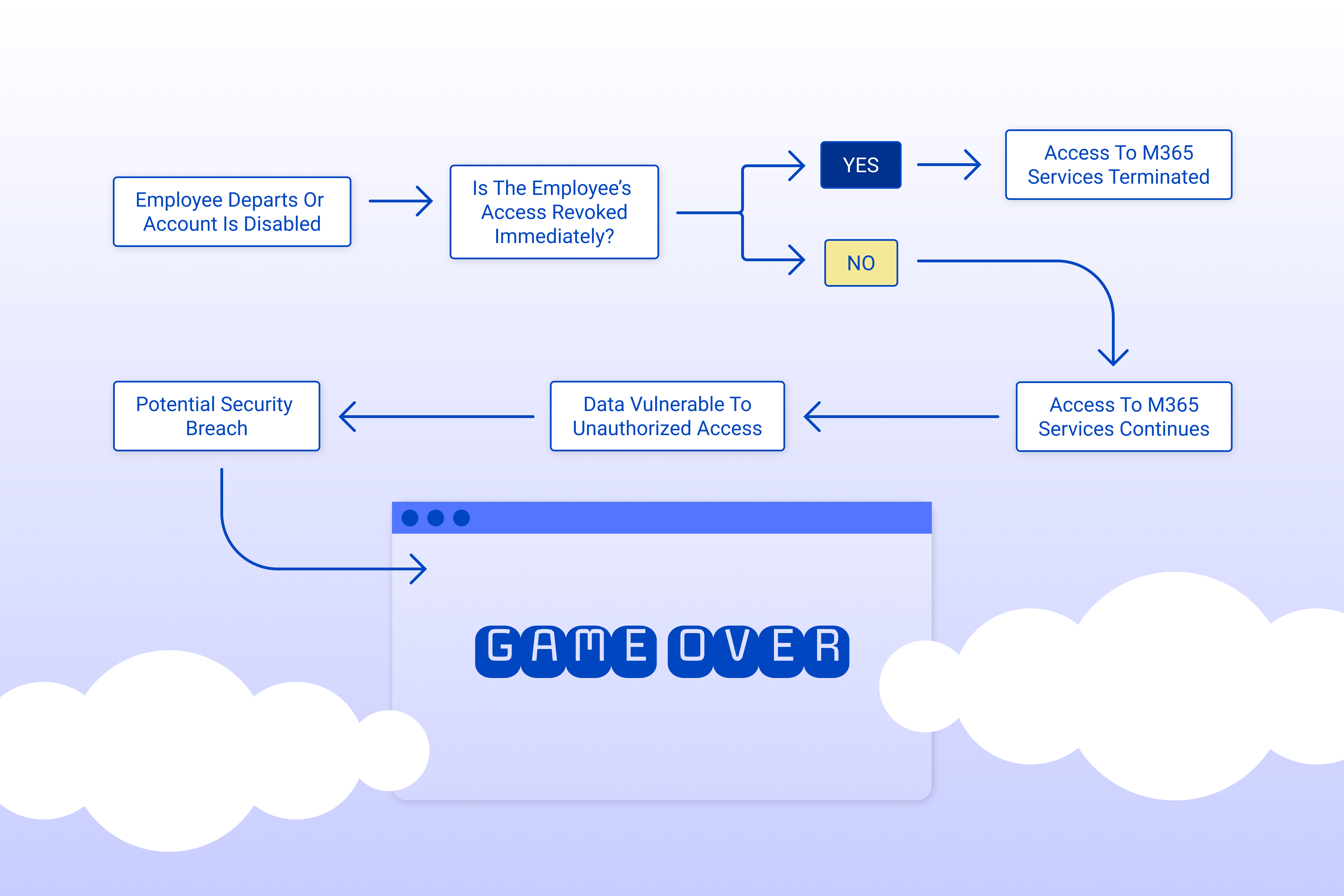
Addressing Misconfigurations in Microsoft 365 and Azure AD
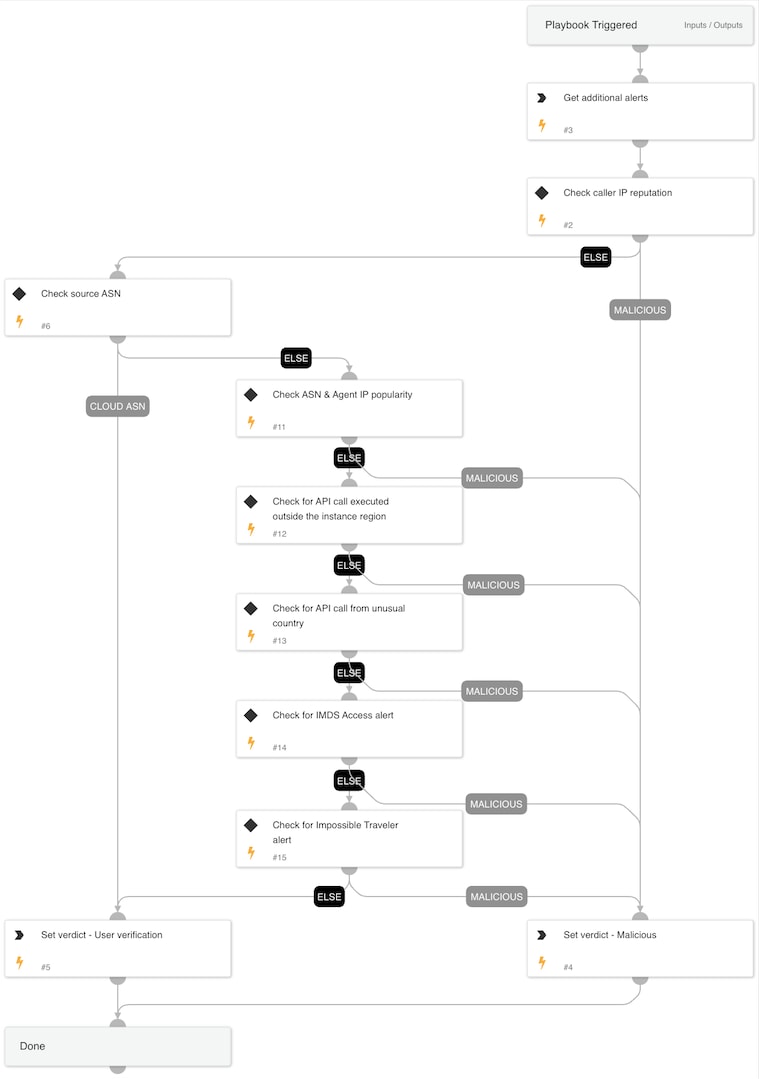
Playbook of the Week: Cloud Token Theft Response - Palo Alto
Unified threat detection for AWS cloud and containers
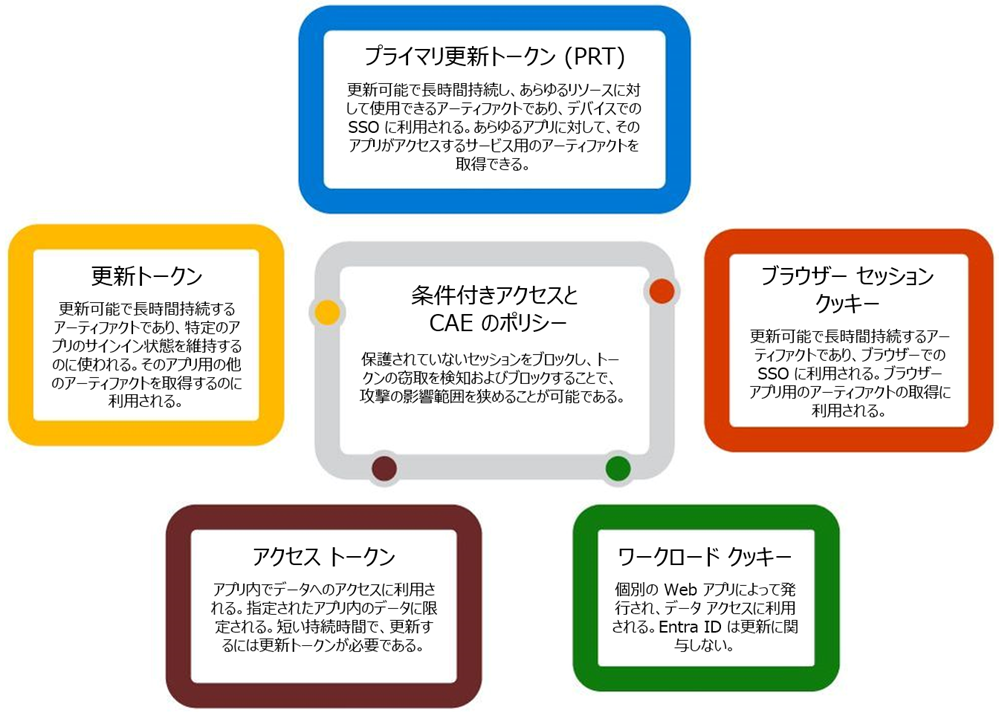
データ流出への対応: トークンの窃取について

Protecting Prospects: How Darktrace Detected an Account Hijack
多要素認証(MFA)を回避するサイバー攻撃が流行、Microsoftが警告:マピオンニュース

Addressing Misconfigurations in Microsoft 365 and Azure AD

Microsoft Incident Response, Author at Microsoft Security Blog
Abuse and replay of Azure AD refresh token from Microsoft Edge in

Jeffrey Appel on LinkedIn: Mind-blowing way to generate KQL: use ChatGPT (OpenAI)

How cyber-attacks take down critical infrastructure
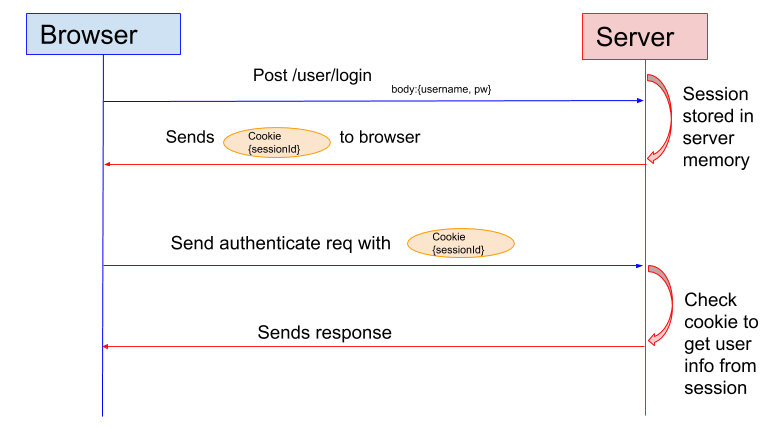
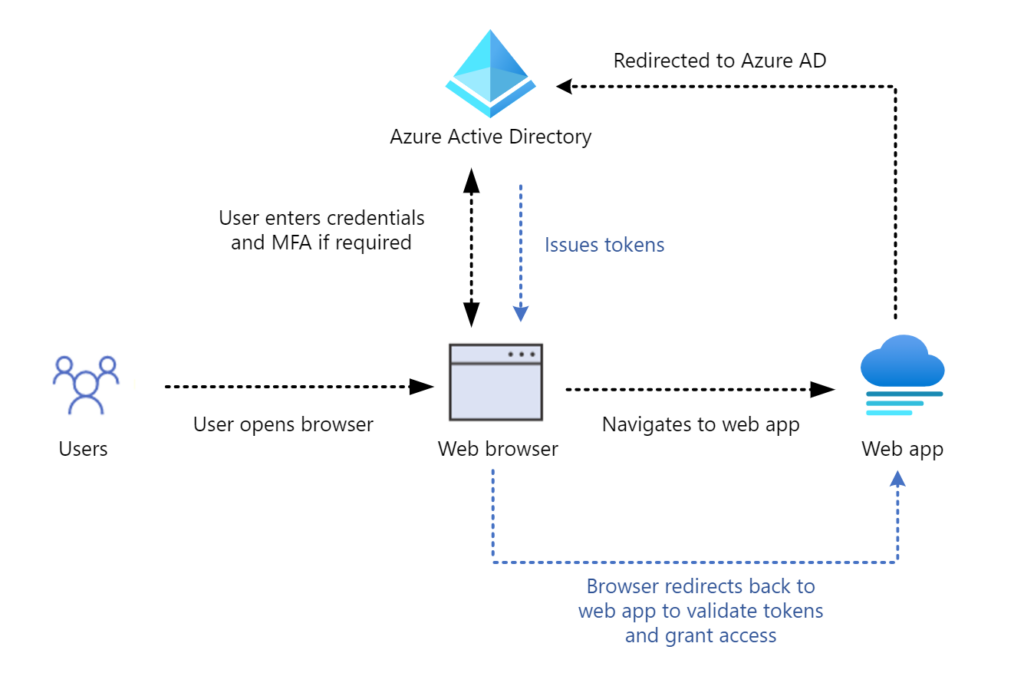
Token-Based Authentication: What Is It and How It Works

What is Token-Based Authentication? Types, Pros and Cons
Recommended for you
You may also like